Russia has some of the best hackers in the world, but in the early days of the war in Ukraine, its ability to create mayhem through malware hasn�t had much of a noticeable impact.
Instead, it�s Ukraine that�s marshalled sympathetic volunteer hackers in an unprecedented collective global effort to make the Kremlin pay for making war on its neighbor. It�s a kind of cyber free-for-all that experts say risks escalating a moment already fraught with extraordinary danger after Russian President Vladimir Putin put his nuclear forces on alert.
So far, Ukraine�s internet mostly works, its president still able to rally global support via a smartphone, and its power plants and other critical infrastructure still able to function. The kind of devastating cyberattacks thought likely to accompany a large-scale Russian military invasion haven�t happened.
�It has not played as large a component as some people thought it might and it definitely has not been seen outside of Ukraine to the extent that people feared,� said Michael Daniel, a former White House cybersecurity coordinator. �Of course, that could still change.�
It�s not clear why Russia hasn�t landed a more powerful cyber punch. Russia might have determined that the impact wouldn�t be serious enough � Ukraine�s industrial base is far less digitized than in Western nations, for one. Or Russia might have determined that it couldn�t do serious harm to Ukraine without risking collateral impact outside its borders.
Many cybersecurity experts believe the Kremlin, at least for now, prefers to keep Ukraine�s communications open for the intelligence value.
Whatever the reasons, the conflict�s early days have been marked by lower-level cyberattacks that appear to be done both by freelancers and state actors.
Prior to the invasion, hackers knocked offline or defaced Ukrainian government websites and wiped some servers with destructive malware. Now, an ad hoc army of hackers � some marshaled online by Ukraine�s SBU security service � are claiming credit for takedowns and defacements of Russian government and media sites.
A volunteer group calling itself the IT Army of Ukraine has more than 230,000 followers on a Telegram channel and is constantly listing targets for hackers to hit, like Russian banks and cryptocurrency exchanges.
On Monday, Ukraine�s SBU made its recruitment of allied volunteer hackers official.
�CYBER FRONT IS NOW OPEN! Help Ukrainian cyber experts hack occupant�s platforms!� it said on its Telegram channel, asking for tips on vulnerabilities in Russian cyber defenses, including software bugs and login credentials.
�It is the first time that states have openly called for citizens and volunteers to cyberattack another state,� said Gabriella Coleman, a Harvard anthropology professor who has charted the rise of hacktivism.
The move mirrors Ukraine�s reliance on its citizens for other areas of defense.
�It shouldn�t be surprising that Ukraine is dipping into all possible resources to fight off the Russians, a much stronger foe. Just like civilians are coming out to fight in the street, it doesn�t surprise me that they are trying to call forward civilians to support this through the digital space,� said Gary Corn, a retired Army colonel who served as general counsel to U.S. Cyber Command.
One hacker group that first appeared last year, the Belarus Cyber Partisans, claimed Monday to have disrupted some rail service in Belarus, the northern neighbor of Ukraine from which several prongs of Russia�s military attacked. The group has been trying to frustrate Russian troop and hardware movements through Belarus.
Sergey Voitekhovich, a former Belarusian railway worker who runs a rail-related Telegram group, told The Associated Press that the Cyber Partisans� digital sabotage Sunday paralyzed train traffic in Belarus for 90 minutes. He said electronic ticket sales were still not functioning as of Monday evening.
The Cyber Partisans hack was intended to disrupt Russian troop movements in Belarus and was the second such action in a little over a month. Voitekhovich said the current attack delayed two Russian military trains bound for Belarus from the Russian city of Smolensk. His story could not be independently verified. Voitekhovich chatted with the AP from Poland. He said police pressure had forced him to leave Belarus.
Pro-Russian ransomware criminals from the Conti gang recently pledged on the group�s dark web site to �use all our possible resources to strike back at the critical infrastructures of an enemy� if Russia was attacked. Shortly afterward, sensitive chat logs that appear to belong to the gang were leaked online.
As partisans on both sides vow more serious cyberattacks, experts say there are real risks of the situation spiraling out of control.
�De-escalation and peace will be hard enough on their own without outsourced hacking to worry about,� said Jay Healey, a cyberconflict expert at Columbia University who has long been opposed to letting the private sector �hack back� against Russian or other state-backed cyber aggression.
Making things more complicated: potential �false flag� operations in which hackers pretend to be someone else when launching an attack, a specialty in cyber conflicts. Attribution in cyberattacks is almost always difficult and could be even more so in the fog of war.
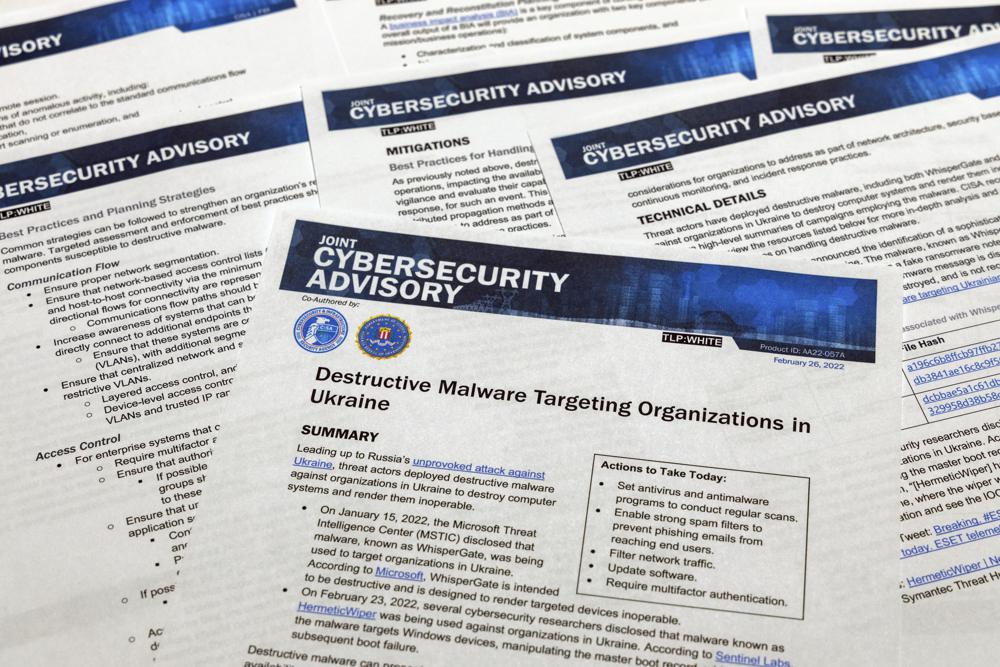
There�s already been some spillover in some cyberattacks. Several hours before Russia�s invasion, destructive cyberattacks hit Ukraine�s digital infrastructure, damaging hundreds of computers with �wiper� malware � including a financial institution and organizations with offices in neighboring Latvia and Lithuania, cybersecurity researchers said.
Microsoft President Brad Smith said in a statement Monday that such attacks on civilian targets �raise serious concerns under the Geneva Convention.�
Smith noted that the cyberattacks � like a series of similar attacks in mid-January � �have been precisely targeted, and we have not seen the use of the indiscriminate malware technology that spread across Ukraine�s economy and beyond its borders in the 2017 NotPetya attack,� referring to a �wiper� that caused more than $10 billion of damage globally by infecting companies that do business in Ukraine with malware seeded through a tax preparation software update.
The West blames Russia�s GRU military intelligence agency for that attack as well some of the other most damaging cyberattacks on record, including a pair in 2015 and 2016 that briefly knocked out parts of Ukraine�s power grid.
So far, there�s not been anything like that in this conflict. But officials say it could be coming.
�I�ve been pleasantly surprised so far … that Russia has not launched more major cyberattacks against Ukraine,� Senate Intelligence Committee Chairman Mark Warner said at an event Monday. �Do I expect Russia to up its game on cyber? Absolutely.�
(AP)